Касперский нашел "звезду смерти" понятно кого, или Equation Group.
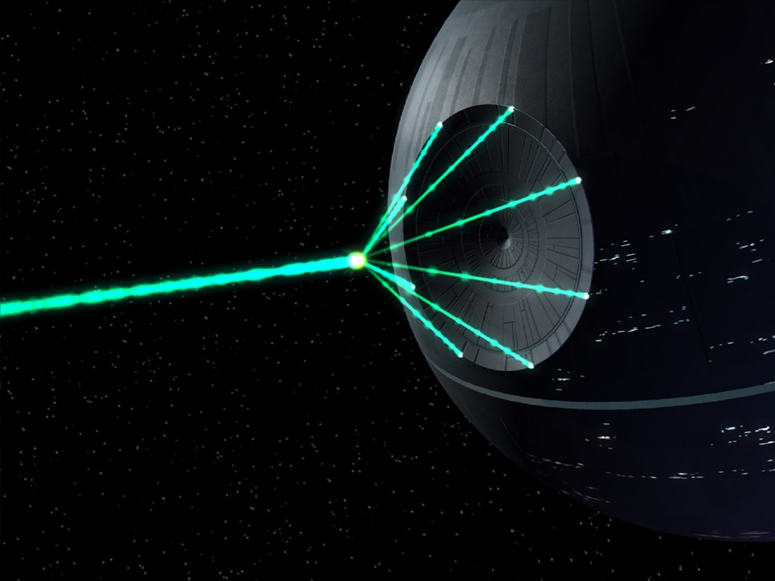
Это, друзья, уже серьезно. Очень серьезно. Причем старую Звезду, та которая с шахтой.
Встречайте EQUATION GROUP, от создателей Stuxnet.
For several years, the Kaspersky Lab Global Research and Analysis Team (GReAT) has been closely monitoring more than 60 advanced threat actors responsible for cyber-attacks worldwide. The team has seen nearly everything, with attacks becoming increasingly complex as more nation-states got involved and tried to arm themselves with the most advanced tools. However, only now can Kaspersky Lab experts confirm they have discovered a threat actor that surpasses anything known in terms of complexity and sophistication of techniques, and that has been active for almost two decades - The Equation Group.
(...)
WHAT MAKES THE EQUATION GROUP UNIQUE?
Ultimate persistence and invisibility
GReAT has been able to recover two modules which allow reprogramming of the hard drive firmware of more than a dozen of the popular HDD brands. This is perhaps the most powerful tool in the Equation group’s arsenal and the first known malware capable of infecting the hard drives.
By reprogramming the hard drive firmware (i.e. rewriting the hard drive’s operating system), the group achieves two purposes:
1. An extreme level of persistence that helps to survive disk formatting and OS reinstallation. If the malware gets into the firmware, it is available to “resurrect” itself forever. It may prevent the deletion of a certain disk sector or substitute it with a malicious one during system boot.
“Another dangerous thing is that once the hard drive gets infected with this malicious payload, it is impossible to scan its firmware. To put it simply: for most hard drives there are functions to write into the hardware firmware area, but there are no functions to read it back. It means that we are practically blind, and cannot detect hard drives that have been infected by this malware” - warns Costin Raiu, Director of the Global Research and Analysis Team at Kaspersky Lab.
2. The ability to create an invisible, persistent area hidden inside the hard drive. It is used to save exfiltrated information which can be later retrieved by the attackers. Also, in some cases it may help the group to crack the encryption: “Taking into account the fact that their GrayFish implant is active from the very boot of the system, they have the ability to capture the encryption password and save it into this hidden area,” explains Costin Raiu.
(...)
Since 2001, the Equation group has been busy infecting thousands, or perhaps even tens of thousands of victims throughout the world, in the following sectors:
Government and diplomatic institutions
Telecoms
Aerospace
Energy
Nuclear research
Oil and gas
Military
Nanotechnology
Islamic activists and scholars
Mass media
Transportation
Financial institutions
Companies developing encryption technologies
Итд.
Краткий релиз:
http://www.kaspersky.com/about/news/virus/2015/equation-group-the-crown-creator-of-cyber-espionage
Полный рапорт:
https://securelist.com/blog/research/68750/equation-the-death-star-of-malware-galaxy/
От себя добавим: это только вторая система серии "Е".
Первую я думаю вспомнят читатели сами.
Все вместе они создают мета-систему.
No Such Agency, угу.